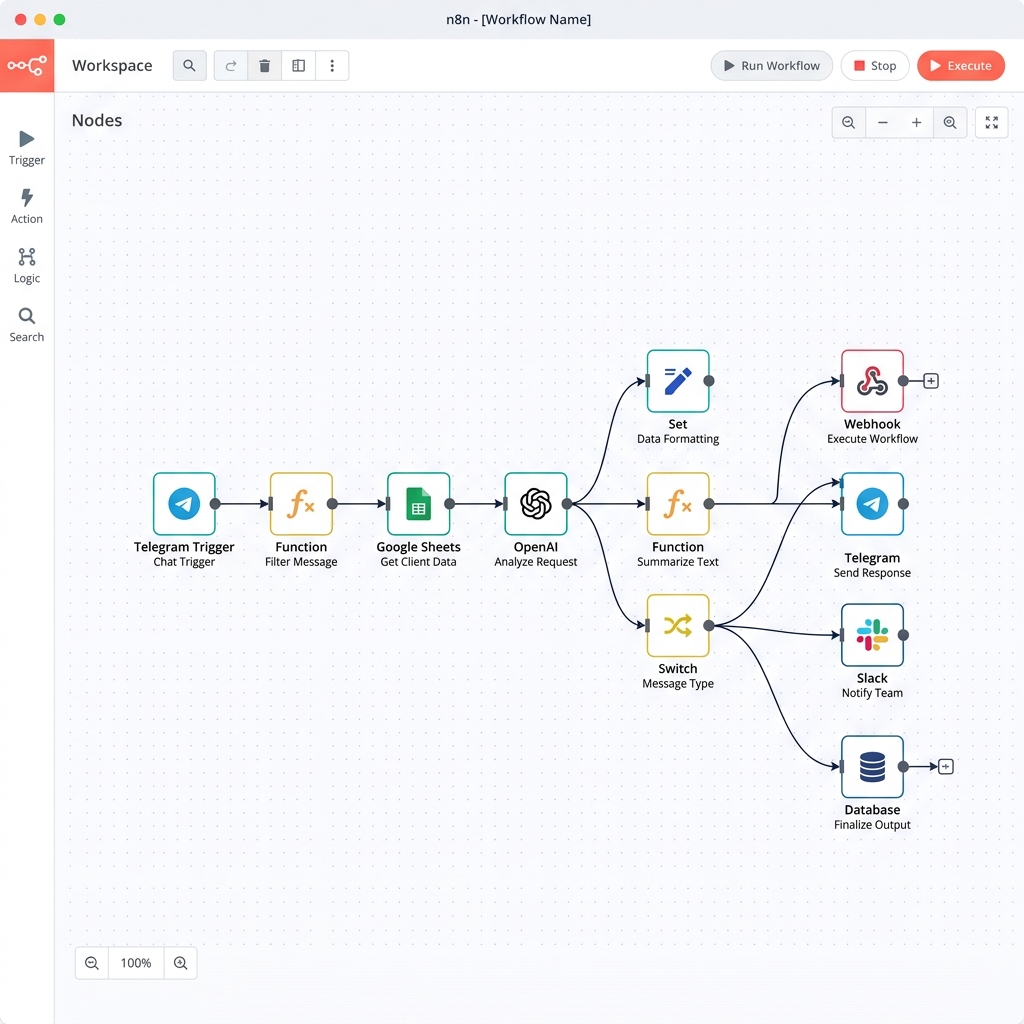
Suspicious Login Detection Workflow n8n Workflow Template
An n8n workflow for detecting suspicious logins using GreyNoise API for IP threat intelligence, IP-API for geolocation, UserParser for user agent analysis, and
Add to Cart - Secure CheckoutInstant Digital Delivery
Product Content & Details
Overview
This professional n8n workflow is designed to automate Suspicious Login Detection Workflow with maximum efficiency and minimal overhead.
Key Features
- Automated Execution: Fully asynchronous processing of tasks.
- Error Handling: Built-in retry logic and error notifications.
- Scalability: Designed to handle high-volume data streams seamlessly.
- Low Maintenance: Self-documenting nodes and clean architectural structure.
How it Works
An n8n workflow for detecting suspicious logins using GreyNoise API for IP threat intelligence, IP-API for geolocation, UserParser for user agent analysis, and Postgres for login history. It prioritizes alerts and notifies via Slack and email for security response.
What's Included?
- Exportable n8n JSON Workflow File
- Implementation Guide & Documentation
- API Configuration Template
Need Custom Implementation?
Don't want to set this up yourself? Hire our elite agency to handle the technical heavy lifting, bespoke design, and SEO execution for your brand.
Explore Our Agency Services →